Cybercrime is on the rise, there is no denying that as hackers get more advanced and the rise in ransom amounts to retrieve stolen data is steadily increasing. Every organization, business, or individual that has a computer, smart phone, or any electronic web-based device or holds sensitive information, data, trade secrets, bank accounts, or intellectual property on a digital file can be a victim of a devastating cybercrime.
Cybercrime is a huge area of concern in today's digital age. It involves theft of sensitive and valuable data using digital assets like computers. The cyber criminals can be very sophisticated with their attacks, very basic or anything in between.
The unfortunate reality is that online platforms are filled with victims just waiting to be scammed, tricked, or fooled into a vulnerable position that they can take advantage of. When it comes to corporate, private sector victim’s, cybersecurity experts find that they are just as likely to fall prey to a cybercrime which can be very costly indeed.
Consider our guide on Preventing Data Loss & Leaks to learn more about staying protected against cyber threats.
What Are The Most Significant Cyber Threats For Local Governments?
There are various cyber threats that regularly prey on local government agencies. Here are two of the most common and damaging threats to be aware of:
1. Insider Threats
In the USA alone there are thousands of institutions that are not prepared or protected from the threats that can strike them at any time, from any computer attacker in the world. One of the most dangerous threats is what is called an Insider Threat: a person in your organization that either purposefully or most commonly, unwittingly opens your system to cyber criminals.
The Insider Threat can be a person in your company that innocently answers a phishing email or the newest scam, the vishing scam (Verbal Phishing via phone call) and provides the cybercriminal with access to your systems, files, customer data, trade secrets, financial assets, or anything else you have stored digitally in the government cloud.
Insider threats can also be employees that purposefully sell your information, or access to your data for a host of reasons including, anger, jealousy, revenge or for profit. In short, it can be anyone, even if you don’t expect it.
- Who In Your Organization Can Act as an Insider Threat?
We see some commonalities when it comes to insider threats. They can be a disgruntled employee, they can be angry with the company for real or imagined slights, they can feel cheated or not valued or they might believe they are undervalued and being used by the company and not properly compensated.
Some employees act as insider threats with a motive for revenge, to get back at a supervisor or owner. Selling valuable data or sensitive information to hackers can help insider threats make a large profit; individuals may want to create their own financial benefit by using blackmail or ransom schemes against their employer.
Lessons learned from previous attacks tell us clearly that anyone with access to your systems is a potential insider threat. To combat this threat, governments have to be aware of the potential damage that can be caused, and develop appropriate policy, procedure, and protocols to fight this expensive criminal enterprise that sees your company as fair game.
2. Ransomware Attacks
Ransomware attacks are the most common cyber threat trending in the United States in 2023. These ransomware attacks are exactly as they sound, cyber criminals attack local government networks or servers to steal data and then attempt to sell it back for a large sum of ransom money.
As you can imagine, the cost to local governments is detrimental when they attempt to retrieve stolen information from hackers, sometimes costing millions. Oftentimes, local governments will attempt to gain back stolen information, pay the demanded ransom from hackers, and then are still unable to recover sensitive government data.
While corporations and small business entities have always been a major target of cybercrime, other organizations such as local government agencies have started to increasingly find themselves victimized, suffering tremendous financial losses from cyber crime attacks every year.
Once we begin to see the scope of this problem, we can see the risk rise. According to recent reports, crucial findings of cybercrime data revealed that 89% of ransomware attacks in 2022 to 2023 resulted in stolen government data. The financial incentive of the ransomware attacks is clear to see as the average government pay out to retrieve stolen data is $327,883.
Learn everything you need to know about how to Keep Data Secure & Prevent Ransomware Attacks with our resource.
Why Isn’t Every Company Prepared to Prevent and Deter Cybercrime?
Unfortunately, like many areas of security preparation, many municipalities don’t see or truly understand the need for a Cybersecurity program, often saying it will never happen to them, or they cannot justify the costs of developing and implementing a proper Cybersecurity program in their company. This kind of thinking can and is very costly to local governments everywhere.
Experts in the field strongly suggest you discuss these growing threats with your government employees and conduct regular cybersecurity training for government employees. At the very least, it is imperative that your local government conducts a cybersecurity threat assessment so you understand the real vulnerabilities you have that hackers may take advantage of.
At this point it should be clear that your municipality is vulnerable to various cyber threats; your local government operations can be severely slowed down or even permanently damaged by Cybercrime, and it is time to do something about that.
What Exactly Can Companies Do To Protect Themselves?
Developing solid policy, procedure, and protocols for all use of company and personal equipment as well as access to company systems and data and ensure passwords are protected. You should also consider these actions:
- Develop a data classification and handling plan and leverage data loss measures for high-risk data.
- Provide all employees, contractors, interns, or anyone else with legitimate access to your systems with training about Phishing, Vishing and Ransomware attacks.
- Develop a remote workers policy for accessing data or computer systems and provide training that makes the concerns of cybersecurity very clear as well as a way for employees to report concerns.
- Conduct thorough background checks on employees, especially people who require access to sensitive data.
- Develop strict data access control protocols, so employees only have access to the information they need.
- Develop a “sign off” policy related to employee access and let them know that all network activity is logged and monitored and that they understand and acknowledge that user accounts and permissions are only for company related business. Set penalties for violations.
- Develop strong internal network and system access permissions for all employees. Access permissions based on Job need should determine what an employee has access to and limit it to that specifically.
- Develop a very strong “Personal Device” policy and make sure that every employee knows the rules and limitations for using their own devices as well as what you consider appropriate work activity. Consider, providing a company owned device for at home or remote workers.
- Develop password policies and user account privileges. Routinely monitor employee accounts and access. Make that all employee accounts and access is canceled when an employee leaves your organization. Consider the timing of this canceling of access to take place before they leave employment to prevent last minute thefts or violations.
Take Action Against Cyber Threats Before It’s Too Late
In a modern digital world, where the very survival of our vital data depends on creating a secure environment for this data, information, trade secrets, and financial assets, we must take the threat of Cybercrime and Insider Threats very seriously and we must take action now, today to protect ourselves.
The next cyber attack is only a keystroke away: phishing scams, vishing scams, or insider threat attacks have the potential to seriously damage your organization or destroy your vital data.
If you have any questions or concerns about Cybersecurity threats you face or for training for your staff, contact at Info@TrueSecurityDesign.com.
Book a consultation with GovPilot to learn more about how modern government software solutions can ensure your locality stays protected from cyber attacks.
Read On:
- GovPilot Moves to Microsoft Cloud, Enhances Cybersecurity for Local Government Customers
- Future of Government: Technology & Public Policy Trends Shaping the Public Sector
- AI in Government in 2023 and Beyond: Bringing Artificial Intelligence to Your Municipality With GovPilot
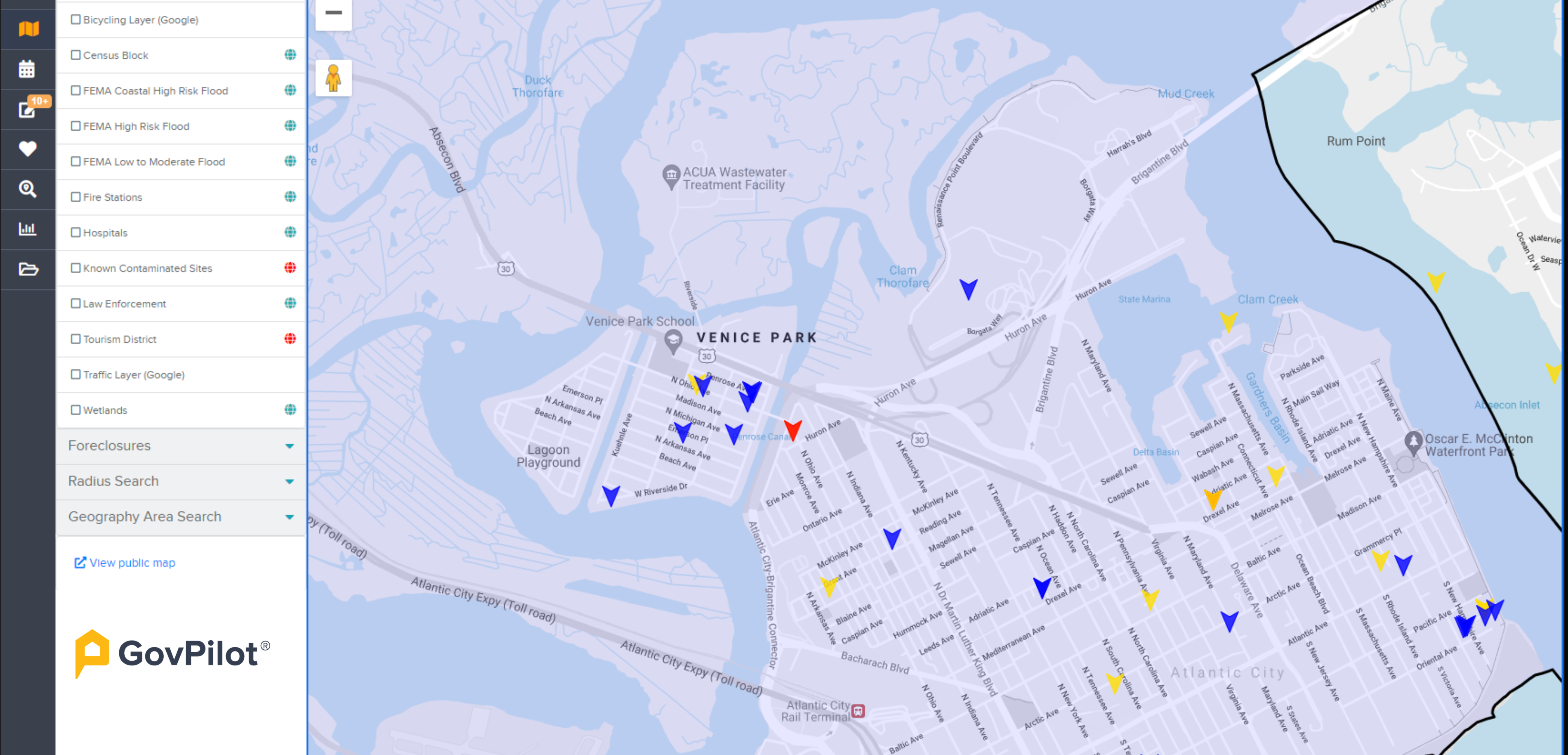
- GIS in Government: How Municipalities Need to Use GIS Maps
Sources:
https://smallbiztrends.com/2019/07/phishing-statistics.html
https://www.nwajtech.com/11-steps-to-mitigate-the-risk-of-phishing-attacks/