Recent ransomware attacks on the Colonial Pipeline and the world’s largest meat supplier have proven how serious of a risk cyber attacks have become. American critical infrastructure, including systems and utilities often under the jurisdiction of local government such as water supplies have become targets of state and non-state actors.
Local governments themselves are no exception. In places like Atlanta, Baltimore, New Orleans, and hundreds of other smaller municipal governments across the U.S. tech-savvy hackers have stolen or locked up critical government data and threatened to destroy it unless paid a hefty ransom. With many municipalities still maintaining unsecure, obsolete on-site servers and IT equipment, hackers know that local governments are an easy, lucrative target.
To make matters worse, even the simplest error like a government worker having a weak password or clicking on a seemingly innocent link in an email can be the thing that leads to a massive cyber breach.
In today's environment of near constant information security threats, the local government workforce is the first line of defense against intrusion by criminals or hostile nations. The internet has made it easier than ever for adversaries from around the world to attack even the smallest municipality, department, or agency. Workers at all levels of government and across departments need to receive cyber security awareness training and establish proper behavior, habits, knowledge, and compliance protocols that can protect critical information and systems.
Consider the following cyber security resources to train your local government officials against ransomware attacks and other cyber threats.
Why Should Government Workers Go Through Cyber Security Training?
Local governments with outdated IT technology are easy targets for a ransomware attack or malware infection. As a result, hackers will hit underprepared government officials with email phishing scams, stolen passwords, or malware to break in and steal confidential and important government data, or lock up critical systems needed for operations and services.
Without proper training, any government official can make the silly but potentially devastating mistake of clicking on a fraudulent email or website link. That’s why it is critical that government employees are aware of the proper ways to prevent cyberattacks, and are continuously kept aware of and engaged in the topic.
You can learn more about the importance of municipal cyber security in our Government Cyber security guide.
What Cybersecurity Awareness Training Should Government Workers Go Through?
Here are some cyber security challenges for local governments that you should train municipal workers in:
-
Train workers to use cloud-based software: governments that use on-site servers to store data are at a much higher risk of being hit with a ransomware attack. That is because they are significantly easier to break into and don’t keep data backed up in the cloud. Switch to easy to navigate cloud-based government management software and quickly train your employees on how to use it so that your data remains secure and recoverable. On-site servers are also much more expensive to maintain and update with security improvements whereas cloud-based systems can automatically be pushed the latest security updates and patches from the provider in real-time.
-
Secure government email systems: make sure that your government email software is secure and that municipal workers strictly use their work emails when conducting government business.
-
Encourage government workers to have strong email passwords: It is astonishing how many people continue to use ‘password’ as their password. Municipal workers should be encouraged to use strong passwords with capital letters, numbers, and signs to prevent hackers from guessing a weak password.
-
Use Two-Factor Authentication: An analysis of the cyberattack on Colonial Pipeline found that the hackers were able to access the company’s network using a compromised username and password that didn’t use multi-factor authentication. Two-factor authentication which will send a code to a user’s personal phone to then be input into a login page, will insure that the person logging into a system is who they say they are and is qualified to do so.
-
Avoid phishing scams: phishing scams are the act of using phony text messages or emails to trick people into clicking on sketchy website links to steal personal information. Here are a few common tactics used by hackers:
-
Suspect emails mentioning vague “suspicious activities”
-
Spoofing email addresses that make the sender appear legitimate but have irregular endings upon closer inspection. For example: mayor@cityofboston.ru (the .ru ending = Russia)
-
Links to an important “report” or document
-
Fake invoices
-
Free coupons to popular products (i.e. “Free Home Depot Gift Card)
-
Asking for personal information or financial information
-
Spear-phishing attacks in which attacker target specific individuals or personas because they might either have less security training and thus more vulnerable - such as a secretary, or are a higher profile target with greater system access - such as a mayor, or city administrator.
-
-
Avoid downloads with malware: sometimes, hackers will bait victims into downloading something like a free song or movie to infect a computer with malware or malicious software. Train government employees to refrain from clicking on or downloading files from untrustworthy links.
-
Utilize official government laptops and devices: make sure that employees are refraining from use of personal computers and phones when conducting government businesses. Government officials should be given personal work computers that are secure and updated with security updates regularly.
-
Use cyber security drills to test government workers: consider sending fake phishing emails and malware downloads to test your government workers. If someone accidentally clicks on a link or downloads a file, it is time to provide a new round of employee training on cyber security best practices, and to remind staff of established rules and regulations.
-
Encourage workers to ask questions: make sure that cyber security is an ongoing conversation within your local government, and that officials feel comfortable asking questions related to cyber security.
-
Training on how to respond if a data breach occurs: taking swift action after a cyber attack occurs is vital to preventing a major breach. Here are the steps that need to be taken immediately after a cyber attack occurs:
-
Have the hacked government worker contact higher-ups about the breach or perceived cyber threat
- Victims of ransomware should report it immediately to The Cybersecurity & Infrastructure Security Agency (CISA) at www.us-cert.gov/report, a local FBI Field Office, or Secret Service Field Office
-
-
-
If necessary, shut down the server believed to be compromised so that the hack doesn’t breach all of the servers
-
Encourage government officials to change their passwords if they encounter suspicious activity or there has been a breech
-
Do NOT pay. Contact Federal authorities for next steps. Paying ransom only encourages future attacks and does not guarantee hackers will grant access to data and systems that they have compromised.
-
What Government Cyber Security Resources Are Available?
Even with the best practices outlined above, there are more advanced resources that leadership in local municipalities should encourage workers to study.
The Cybersecurity & Infrastructure Security Agency (CISA) provides a number of free resources, training, and security assessments to State, Local, and Tribal governments. Among these free services from CISA is a free cyber hygiene assessment which includes several scanning and testing services to help organizations reduce their exposure to threats by taking a proactive approach to mitigating attack vectors.
-
Vulnerability Scanning: Evaluates external network presence by executing continuous scans of public, static IPs for accessible services and vulnerabilities. This service provides weekly vulnerability reports and ad-hoc alerts.
-
Web Application Scanning: Evaluates known and discovered publicly-accessible websites for potential bugs and weak configuration to provide recommendations for mitigating web application security risks.
-
Phishing Campaign Assessment: Provides an opportunity for determining the potential susceptibility of personnel to phishing attacks. This is a practical exercise intended to support and measure the effectiveness of security awareness training.
-
Remote Penetration Test: Simulates the tactics and techniques of real-world adversaries to identify and validate exploitable pathways. This service is ideal for testing perimeter defenses, the security of externally-available applications, and the potential for exploitation of open source information.
The Federal Virtual Training Environment (FedVTE) is a free cyber security training program for government workers at all levels. It addresses many of the cyber security challenges for state and local government officials and offers in-depth resources on things like cyber security basics, emerging cyber security threats, cloud computing security, and more.
Proper employee behaviors are a critical component of establishing cybersecurity and data privacy for your government and constituents. While there is no magic bullet to defeat cybersecurity threats, regular cybersecurity training programs for all staff and a transition away from outdated on-site servers toward a cloud-based digital transformation can provide a layer of security that is needed in a world of increasing cyber attacks.
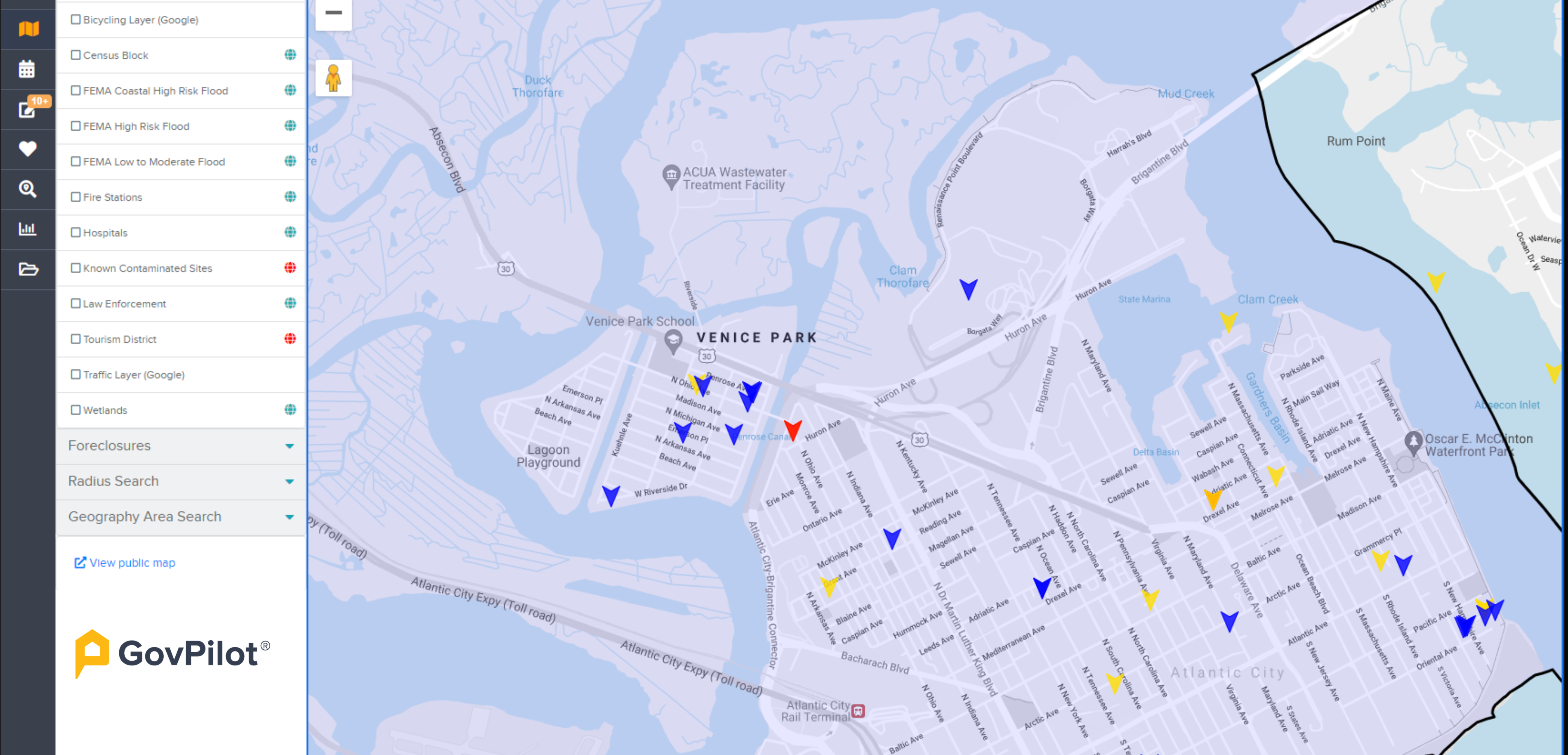
In speaking with GovPilot customers, local government employees from across the country have reported that it takes little time to get trained and feel confident using cloud-based software. That means on top of having better processes for things like zoning permits and business licenses, your well-trained employees will also be keeping government data secure.
To learn more about how local government software can keep your municipal or county government secure, improve workflows, and provide convenient digital constituent services schedule a free consultation.
Ensure that your local government is one with a Local Government Cybersecurity Management Plan to take control of cybersecurity measures in your municipality, before an emergency happens. Base your plan off of the successful cybersecurity management plan that New York recently deployed.
Cybersecurity Awareness Training FAQs
1. What is cybersecurity awareness training?
Security awareness training is the process of providing formal cybersecurity education to your workforce about a variety of information security threats and your government's policies and procedures for addressing them.
2. Why is cybersecurity awareness training important for local governments?
Local governments with outdated IT technology are easy targets for a ransomware attack or malware infection. As a result, hackers will hit underprepared government officials with email phishing scams, stolen passwords, or malware to break in and steal confidential and important government data, or lock up critical systems needed for operations and services. Employees and government officials are the first line of defense agains cyber threats. It is essential that employees at all levels of local government understand how to detect and avoid possible cyber threats, and what to do should they discover a vulnerability or compromise.
3. What Federal Agencies can help secure local governments before or after a cyber attack?
Local government officials should establish a working relationship with The Cybersecurity & Infrastructure Security Agency (CISA) which provides resources and services free of charge to state, local, and tribal governments. Additionally, local governments should be prepared to report any malicious cyber activity to their nearest FBI and Secret Service Field office who can help elevate to the proper authorities.